AWS-Vault helps reduce one of the most common AWS security mistakes: leaving long-lived IAM access keys in plaintext credentials files or shell history. Instead, it stores the bootstrap credential in an operating-system secure backend and then creates short-lived sessions for the AWS CLI or Management Console.
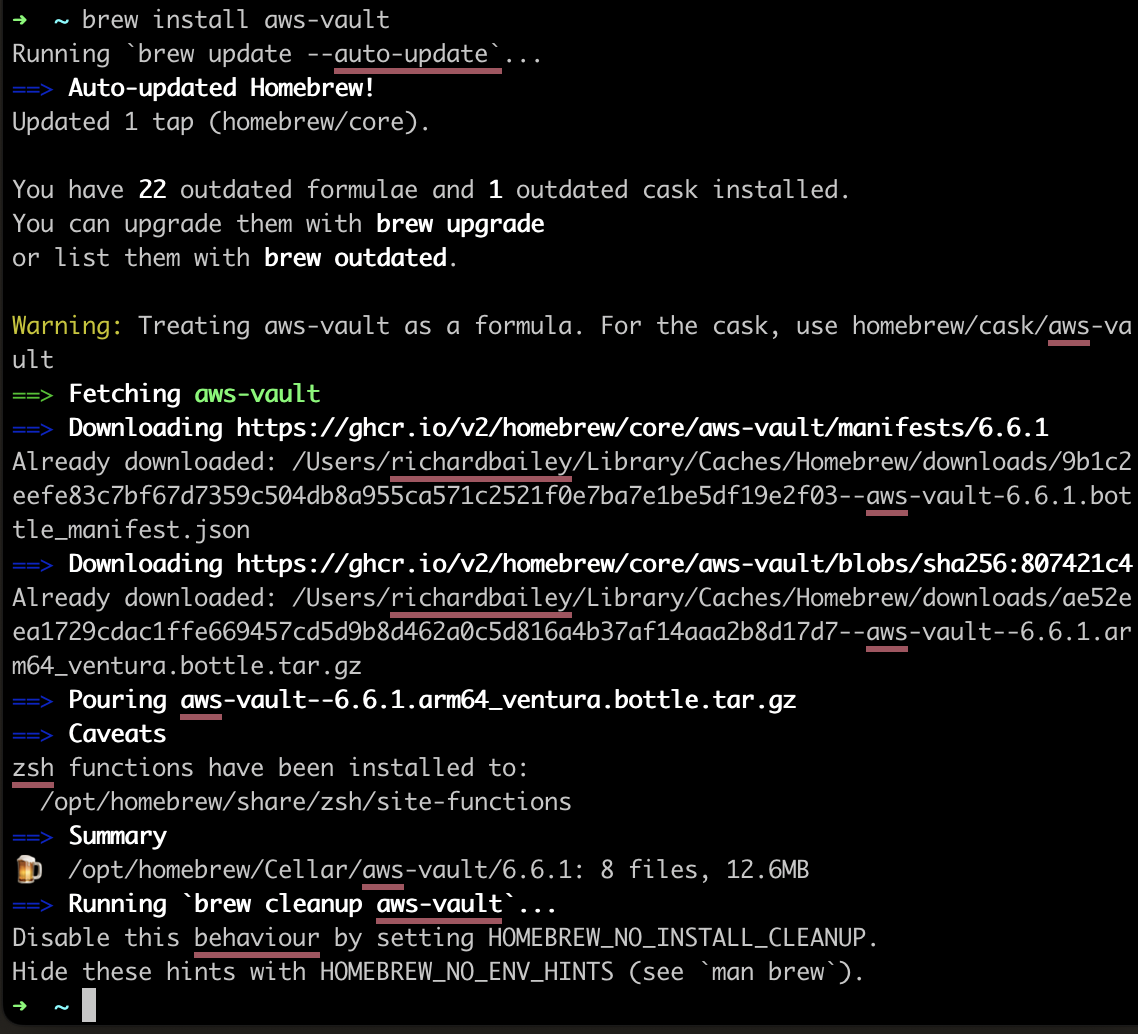
This page focuses on the security model and the most important hardening steps. If you need setup instructions first, start with AWS-Vault Guide: Install, Configure, and Use It Securely, and then return here.
What AWS-Vault improves
- It moves the bootstrap AWS credential into an operating-system secure backend such as macOS Keychain, Windows Credential Manager, or a Linux keyring backend.
- It encourages the use of temporary role sessions instead of permanent access keys for daily work.
- It supports MFA within the normal operator workflow rather than treating it as an afterthought.
- It reduces the temptation to export credentials manually into long-lived shell environments.
What AWS-Vault does not solve
- It does not fix weak IAM design or over-privileged roles.
- It does not replace fleet management, disk encryption, or endpoint protection on developer laptops.
- It does not eliminate the risk of long-lived bootstrap keys if your issuance process is too broad.
Security best practices for AWS-Vault
Keep the Bootstrap user minimal
The IAM user created by AWS-Vault should usually be used to assume roles, not to perform privileged day-to-day work directly. Give it the narrowest practical permission set and use role assumption for actual admin or deployment access.
Prefer role profiles and temporary sessions
Use AWS-Vault to store the base profile, then run commands through a role profile with aws-vault exec. This keeps the long-lived credential in the secure backend and the actual working session temporary.
aws-vault add dev
aws-vault exec dev-admin -- aws sts get-caller-identityEnforce MFA
If the target role requires MFA, keep the mfa_serial value in your AWS config and make MFA prompts part of the normal workflow instead of a break-glass exception.
Protect the workstation and secure store
The secure backend only helps if the workstation is protected. Use full-disk encryption, a strong local login, and short screen-lock timeouts. On Linux, choose a backend you actually manage securely instead of falling back to an ad hoc file workflow.
Audit and rotate
Review stored profiles, unused bootstrap users, and old role assumptions regularly. If an engineer no longer needs a profile, remove it with aws-vault remove <profile> and rotate the underlying IAM user credential if appropriate.
Keep security guidance aligned with your access model
If your organisation has already standardised on workforce federation, IAM Identity Center is often the stronger long-term security model because it avoids distributing long-lived IAM-user access keys as the bootstrap mechanism.
Practical checklist
- Store only minimal bootstrap credentials in AWS-Vault.
- Run daily work through role profiles with
aws-vault exec. - Require MFA for privileged roles.
- Protect the workstation and secure the backend with strong local controls.
- Remove unused profiles and rotate old bootstrap credentials.